Implementing Hardware-Based Security Using Physically Unclonable Functions
Cryptography is still a relevant technique today, but it isn't as perfect as far as hardware security is concerned. Physical unclonable functions (PUFs) have emerged as a more foolproof way to build security into hardware. Read on to learn more about using dynamic random access memory (DRAM) PUFs for hardware-based security implementations like random cryptographic key generation and device authentication (anti-counterfeiting).
Introduction to Physical Unclonable Functions
Hardware-rooted security is an active area of research and has led to numerous important innovations, including PUFs. To create PUFs, designers tap into the inherent differences in physical device characteristics to generate unique responses that can't be copied to or replicated in counterfeited devices. Some of the inherent IC variations are path delays and voltage gain. Each IC ever produced exhibits unique characteristics, making it physically different from any other. Once you have figured out the random attributes for a specific device, you can use those to create a unique cryptographic key. The key for each device is naturally random but can be reproduced for hardware authentication and other security purposes.
How PUF Hardware-Based Security Works
Device authentication with PUFs is a "challenge-response" kind of system. It works as follows:
- Challenge- Manufacturer puts the PUF to a series of "challenges."
- Response-Manufacturer observes and records the response to each input challenge.
- Implementation-A counterfeit wouldn't "pass" any of the manufacturer's challenges as it would produce its own unique responses, deviating from the recorded ones.
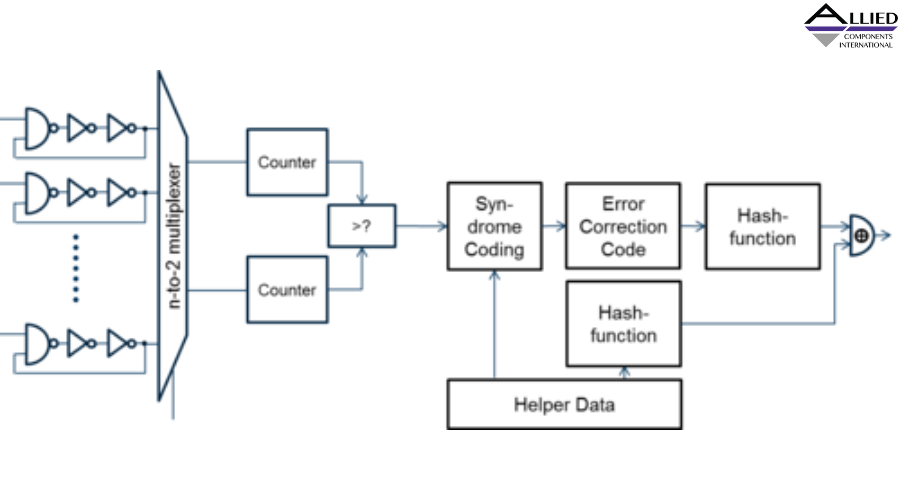
DRAM PUF Hardware-Based Security Implementation
It's possible to create DRAM PUFs by leveraging variations in DRAM cell charge leakage rates. During manufacture, the PUF will be fed with a binary value. The manufacturer will then measure and record the value of the DRAM cells array after a specific time interval. Unique variations in the cells' charged/discharged states are to be expected. These responses can be stored on a database and used to authenticate devices or generate cryptographic keys.
PUFs Device Security Advantages
Physically unclonable functions offer numerous advantages over standard cryptographic techniques, including:
- Unreadable device identifiers- Standard cryptographic methods store unique keys in non-volatile physical memories. If a bad actor breached the storage, they could read the unique device identifiers. Despite PUFs being non-volatile memory techniques, they don't store their unique IDs in a physical location. They generate the random numbers on demand, such as during device authentication. IDs created this way are more difficult to view and decipher.
- Natural hardware-based security options-PUFs are ideal for building hardware-rooted security, such as in ICs. As the unique IC identifiers are based on natural variations in component characteristics, they are difficult for bad actors to reproduce through deterministic or other approaches.
Hardware security designers have a highly effective, versatile tool on hand—physical unclonable functions. Thanks to its ability to generate hard-to-read, unique, random keys, PUF technology can be used to build security into devices and make them difficult to "clone." If you're interested in highly efficient electronic/magnetic devices, visit our Allied International Website now.